How to Remove EXIF Data from Images: The Complete 2026 Guide
EXIF data can reveal your camera model, GPS location, shooting settings, and AI generation parameters. This comprehensive guide covers every method for removing EXIF data from JPEG, PNG, WebP, and HEIC images.
Senior Software Engineer, Image Processing
In This Article
- 01What Information Does EXIF Data Contain?
- 02EXIF Storage Across File Formats
- 03Methods for Removing EXIF Data
- 04Verifying EXIF Removal
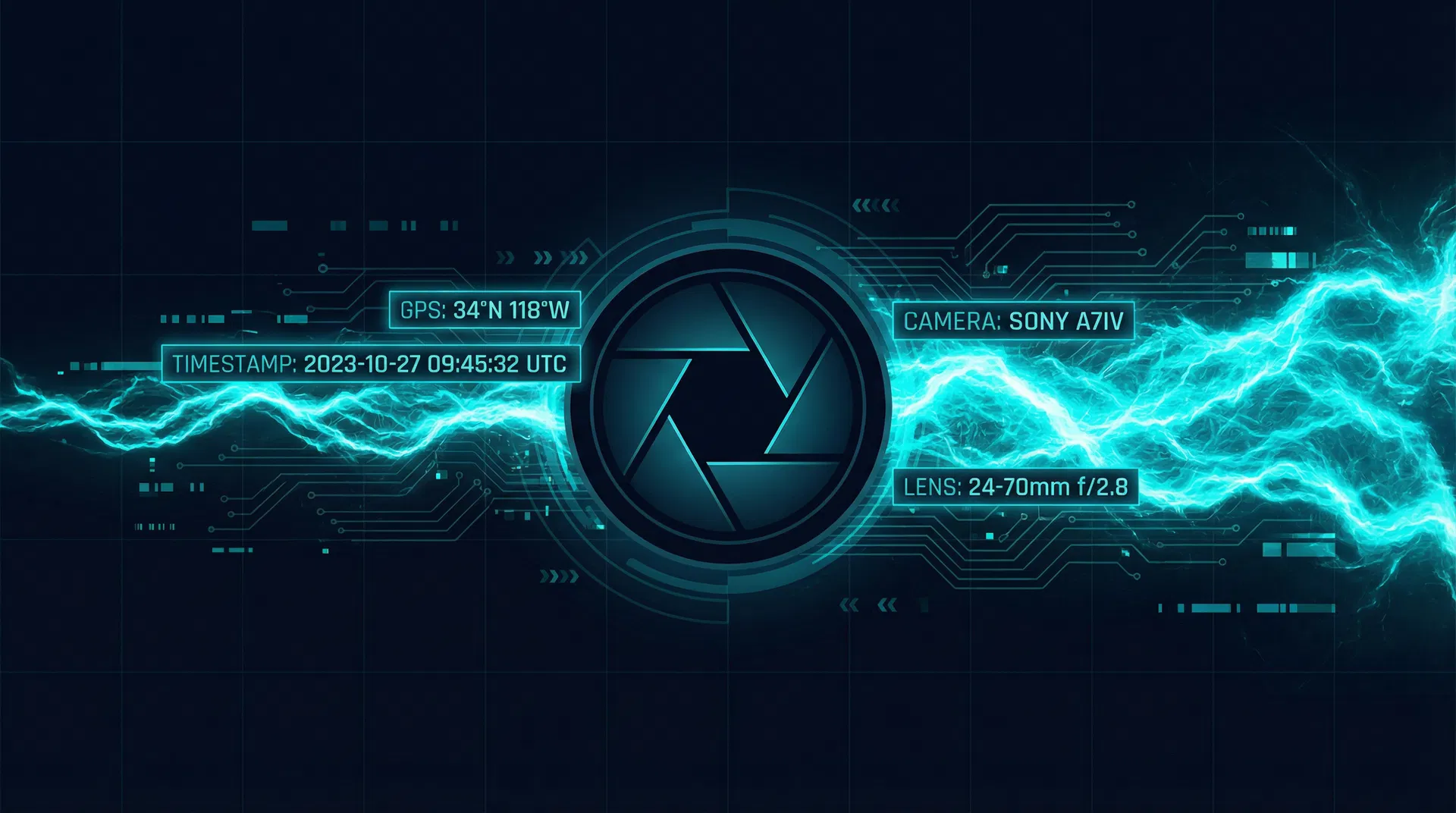
EXIF data is the invisible passenger in every digital image. Originally designed to help photographers review their camera settings after a shoot, EXIF has evolved into a comprehensive record of how, when, and where an image was created — and in the age of AI image generation, it has become a detailed log of which AI tool you used and exactly how you used it. Removing EXIF data is one of the most important privacy practices for photographers, AI creators, and anyone who shares images online.
This guide covers everything you need to know about EXIF data in 2026: what information it contains, which file formats store it, why it matters for both privacy and AI detection, and the most effective methods for removing it across different platforms and use cases.
What Information Does EXIF Data Contain?
The EXIF standard defines hundreds of possible data fields, though not all are used in every image. For photographs taken with a camera or smartphone, the most privacy-sensitive fields include GPS coordinates (latitude, longitude, altitude, and sometimes speed and direction), the device make and model, the serial number of the camera body, the date and time of capture (which can be cross-referenced with your location history), and the software used to process the image.
For AI-generated images, the relevant EXIF fields are different. The Software field typically contains the name and version of the AI tool. The UserComment field is frequently used to store the full generation prompt. The ImageDescription field may contain model parameters. Stable Diffusion images in particular are notorious for embedding the complete generation parameters — including the prompt, negative prompt, model checkpoint, seed, steps, CFG scale, and sampler — in the PNG tEXt chunks or EXIF UserComment field.
| EXIF Field | Typical Content | Privacy Risk |
|---|---|---|
| GPSLatitude / GPSLongitude | Precise coordinates where photo was taken | Very High |
| Make / Model | Camera or phone manufacturer and model | Medium |
| Software | AI tool name and version (e.g., 'Stable Diffusion 3.5') | High (AI detection) |
| UserComment | Full AI generation prompt | Very High (AI detection) |
| DateTimeOriginal | Exact timestamp of creation | Medium |
| SerialNumber | Camera body serial (links images to a device) | High |
| Artist / Copyright | Creator name and copyright statement | Low-Medium |
| ImageDescription | AI model parameters, LoRA weights | High (AI detection) |
EXIF Storage Across File Formats
EXIF data is not stored identically across all image formats, which is why different removal methods have different effectiveness depending on the file type you are working with.
JPEG Files
JPEG stores EXIF data in an APP1 marker segment near the beginning of the file. This is a well-defined binary structure that most metadata tools can read and write reliably. Removing EXIF from JPEG is straightforward: the APP1 segment can be deleted without affecting the image data. However, JPEG files may also contain XMP data in a separate APP1 segment (distinguished by a different identifier), IPTC data in APP13, and C2PA credentials in APP11. A complete metadata removal must target all of these segments.
PNG Files
PNG uses a chunk-based structure where metadata is stored in named chunks interspersed with image data chunks. The relevant metadata chunks are tEXt (uncompressed text key-value pairs), iTXt (UTF-8 encoded text, often used for XMP), zTXt (compressed text), and eXIf (EXIF data in a dedicated chunk, added in PNG 1.6). Stable Diffusion and ComfyUI make heavy use of tEXt chunks to store generation parameters. PNG metadata removal requires iterating through all chunks and selectively removing non-image chunks.
WebP and AVIF Files
WebP files use a RIFF container format with EXIF and XMP data stored in dedicated 'EXIF' and 'XMP ' chunks. AVIF files, being based on the ISOBMFF container, store metadata in 'meta' boxes. Both formats are less commonly used for AI-generated images in 2026, but support for them is increasingly important as WebP becomes the default output format for some AI tools and AVIF adoption grows.
HEIC Files (iPhone Photos)
HEIC (High Efficiency Image Container) is the default photo format on iPhones and is based on the same ISOBMFF container as AVIF. HEIC files can contain extensive metadata including GPS data, device information, and Apple-specific metadata. When iPhone users use AI editing tools (like Apple Intelligence or third-party apps), AI-related metadata may be added. HEIC metadata removal requires ISOBMFF-aware tools.
Methods for Removing EXIF Data
Method 1: Browser-Based Tools (Recommended)
Browser-based tools that use the HTML5 Canvas API are the most privacy-preserving option for EXIF removal. Because the Canvas API only works with pixel data, drawing an image onto a canvas and exporting it creates a new file with no metadata of any kind. This approach works for JPEG, PNG, WebP, and (with conversion) HEIC files. The key advantage over server-based tools is that your original files never leave your device.
BlankAI uses the Canvas API to strip all EXIF data from JPEG, PNG, WebP, AVIF, and HEIC images directly in your browser. It also removes C2PA credentials and applies pixel-level fingerprint modification — all without uploading your files.
Remove EXIF Data Free →Method 2: ExifTool (Command Line)
ExifTool by Phil Harvey is the gold standard command-line tool for metadata manipulation. The command 'exiftool -all= -overwrite_original filename.jpg' removes all metadata from a JPEG file. For PNG files with Stable Diffusion parameters, 'exiftool -all= -PNG:all= filename.png' is more thorough. ExifTool is free, open-source, and available for Windows, macOS, and Linux. Its main limitation is that it requires technical comfort with the command line and does not remove C2PA credentials by default.
Method 3: Operating System Built-in Tools
Windows 10 and 11 include a built-in EXIF remover accessible through File Explorer: right-click an image, select Properties, go to the Details tab, and click 'Remove Properties and Personal Information.' This removes most EXIF fields but is not comprehensive — it misses some fields and does not handle PNG text chunks or C2PA data. macOS Preview can export images without metadata using File > Export, but again, this is not complete metadata removal.
Verifying EXIF Removal
After removing EXIF data, always verify the result before using the image. The most reliable verification method is to use ExifTool with 'exiftool -a -u -g1 filename.jpg' — this shows all metadata in all groups. A successfully cleaned image should show only minimal output, typically just the file type and basic image dimensions. Online tools like exifinfo.org or Jeffrey's Exif Viewer can also display EXIF data in a readable format for quick verification.
BlankAI's processing results panel shows you exactly which metadata fields were detected and removed, along with the SHA-256 hash before and after processing. You can also use BlankAI's Image Diff tool to compare the original and cleaned images side-by-side and verify that the hash has changed.
Remove EXIF data, GPS coordinates, AI generation parameters, and C2PA credentials from up to 20 images at once — free, private, and instant.
Try BlankAI FreeShare this article
Marcus Webb
Senior Software Engineer, Image Processing
Marcus Webb is a software engineer specializing in image processing pipelines and browser-based cryptography. With over a decade of experience building media tools at scale, he has contributed to open-source projects including ExifTool and libvips. He writes about the technical realities behind metadata standards and their privacy implications.